SoumniBot: Android Malware with Evasive Tactics
A new type of banking malware for Android, named “SoumniBot,” employs an unconventional obfuscation method that leverages vulnerabilities in the process of extracting and analyzing the Android manifest. This allows it to circumvent standard security measures and execute information theft operations.
The method was identified and analyzed by specialists at Kaspersky Lab, who revealed the technical details of how the malware exploits Android’s features for analyzing and extracting APK manifests.
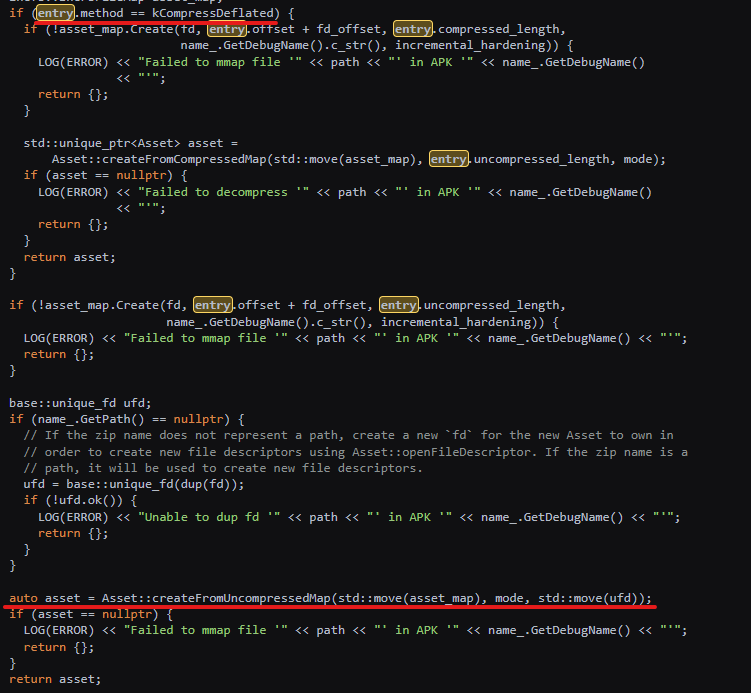
Manifest extraction procedure
“Any APK file is a ZIP archive with AndroidManifest.xml in the root folder. This file contains information about the declared components, permissions and other app data, and helps the operating system to retrieve information about various app entry points. Just like the operating system, the analyst starts by inspecting the manifest to find the entry points, which is where code analysis should start,” explains researcher Dmitry Kalinin.
“This is likely what motivated the developers of SoumniBot to research the implementation of the manifest parsing and extracion routine, where they found several interesting opportunities to obfuscate APKs,” the specialist continues.
SoumniBot’s distinguishing feature is the use of three different methods of manipulating the manifest file—altering its size and compression—to evade parser checks.
- The first method involves using an invalid compression value when unpacking the APK manifest, allowing it to bypass standard security checks.
- The second method involves incorrectly specifying the file size of the manifest, and misleading code analysis tools by adding extraneous data during the copying process.
- The third method involves using excessively long strings for XML namespace names in the manifest, which complicates automated analysis.
Kaspersky Lab has informed Google about the deficiencies of the official APK Analyzer utility when working with files using the aforementioned bypass methods.
According to the data obtained, SoumniBot, once installed, requests configuration parameters from a predefined server while simultaneously sending it information about the infected device, including the phone number, mobile operator used, and other data.
The malware then launches a service that restarts every 16 minutes and transmits data from the smartphone every 15 seconds. The stolen data includes IP addresses, contact lists, account details, SMS messages, photographs, videos, and digital certificates for online banking.
Data management is conducted through an MQTT server, which can also send commands to the smartphone, leading to the following actions:
- deletion or addition of contacts;
- sending SMS messages;
- adjusting the ringtone volume;
- turning silent mode on or off;
- enabling or disabling the device’s debug mode.
SoumniBot primarily targets Korean users of mobile banking. Like many malicious Android apps, after installation, it remains active in the background while concealing its icon. This significantly complicates the detection and removal of the malware, especially for inexperienced users.
Kaspersky Lab’s report provided a necessary list of compromise indicators, including hashes for the malware and two domains used by the malware operators for C2 server operations.





