New XLoader Variant Installs & Attacks Silently on Android
Cybersecurity experts at McAfee have discovered a new iteration of the malicious XLoader software, capable of autonomously initiating on infected Android smartphones upon installation. This revelation poses a significant threat to users across the United States, the United Kingdom, Germany, France, Japan, South Korea, and Taiwan.
XLoader, also known as MoqHao, previously recognized as one of the most perilous types of malware for Android, now operates stealthily in the background, extracting sensitive data including photographs, text messages, contact lists, and device hardware information.
The malware’s dissemination occurs via deceptive links sent in text messages, directing to APK files that circumvent the Google Play store, thereby elevating the risk of malware infection. Google has actively combated this distribution method by implementing Google Play Protect scanning and permission controls for third-party APK files.
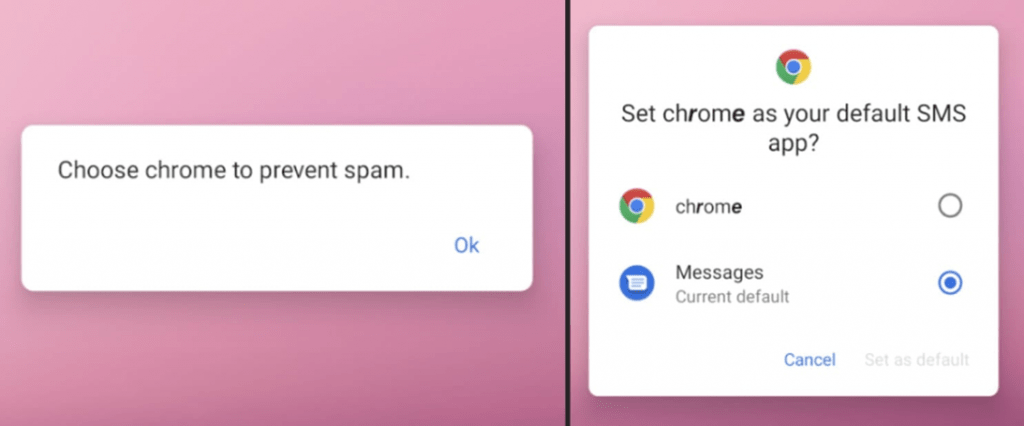
In the current XLoader campaign, the malware disguises itself as Google Chrome, enticing users to install it as their primary SMS application to prevent spam, and employing various languages in its messages to appear more credible.

Furthermore, the new XLoader variant features an auto-launch function post-installation, rendering the mere act of application installation perilous, as the malware autonomously activates and commences its malicious activities. Unlike most malware that requires manual execution to begin the infection chain, XLoader also possesses the ability to propagate itself by sending an SMS with short links to its installation to all contacts in the victim’s phone book.
Since its emergence in the mobile threat landscape in 2015, XLoader has consistently refined its attack methodologies, enhancing its stealth capabilities and efficacy. McAfee warns that the latest variants of XLoader could be particularly effective due to their minimal user interaction requirement.
To safeguard against Android malware, it is advised to refrain from installing applications from unofficial sources, not to open URLs from SMS messages, even from familiar senders, and to scrutinize the permissions granted to applications. Limiting the number of installed applications and relying only on those developed by verified developers is also recommended.





