Microsoft BitLocker no longer uses hardware-based encryption by default
Last year, security researchers found that most SSD hardware encryption schemes have weaknesses and are easily cracked. These embedded hardware encryptions are easily broken due to defects. This problem will also bring great security risks to enterprises and high-security environment. At that time, Microsoft quickly issued an announcement to guide users to switch to software-based encryption. The so-called software encryption refers to the use of BitLocker built-in algorithm to encrypt the hard disk, that is, directly ignore the hardware encryption that comes with the SSD.
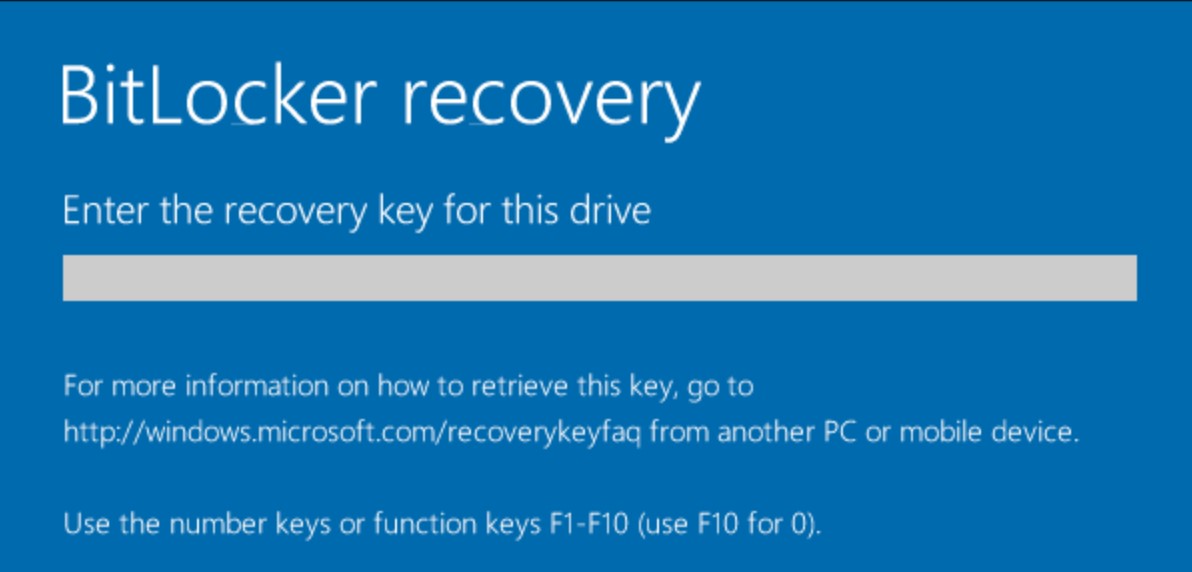
In the latest release of the Windows 10 Insider Previews Build 18317, the BitLocker Encryption Group Policy configuration has been replaced by software-based encryption by default. Users do not need to make any configuration to use software encryption instead of hardware encryption by default, which is effective for preventing hard disk encryption from being cracked.
Of course, if the user needs it, we can change the hardware encryption through Group Policy, but the user needs to determine that his hard disk hardware encryption is not defective. This defect is currently only found to affect SSDs such as Samsung, and users using mechanical hard drives can continue to use hardware encryption or software encryption.
Microsoft said, “Microsoft is aware of reports of vulnerabilities in the hardware encryption of certain self-encrypting drives (SEDs). Customers concerned about this issue should consider using the software only encryption provided by BitLocker Drive Encryption. On Windows computers with self-encrypting drives, BitLocker Drive Encryption manages encryption and will use hardware encryption by default.”





