Linux Kernel 5.8 will introduce inline encryption support for blk-mq
In order to provide better encryption performance, Google engineers are currently adding inline encryption support to the Linux file system encryption management tool, fscrypt. The development related to this includes the introduction of inline encryption in the Linux 5.8 block device queue management blk-mq.
fscrypt is an advanced tool for encryption management of Linux file systems. It manages metadata, key generation, key encapsulation, and PAM integration, and provides a unified interface for creating and modifying encrypted directories. The kernel part of fscrypt has been integrated into a file system such as ext4.
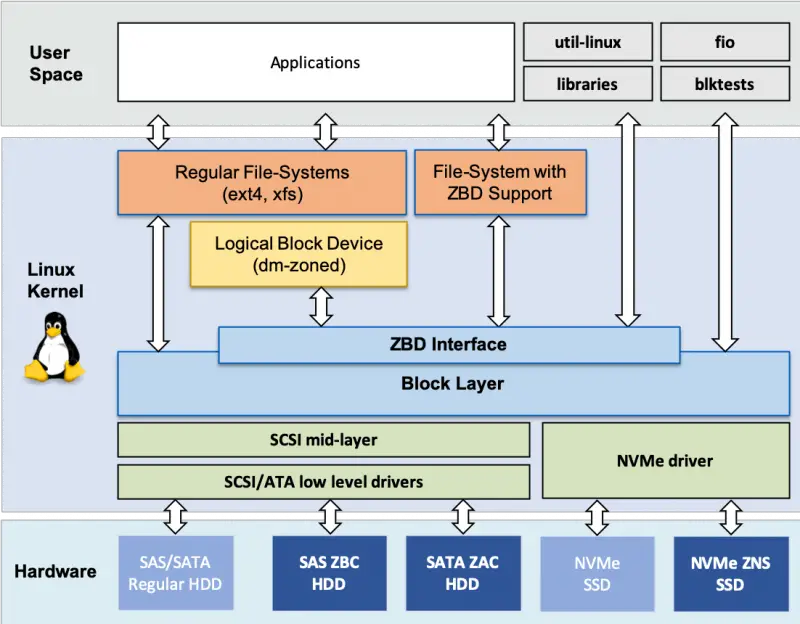
blk-mq is Linux’s block device layer multi-queue mechanism. It changes the single queue of the request layer in the Linux kernel storage stack to multi-queue, theoretically improving performance.
If the next blk-mq supports inline encryption, then it can pass the encryption context down the storage stack, which is currently explained in the Linux kernel source commit: “We also make changes to blk-mq to make it handle bios with encryption
contexts. blk-mq can merge many bios into the same request. These bios need to have contiguous data unit numbers (the necessary changes to blk-merge are also made to ensure this) – as such, it suffices to keep the data unit number of just the first bio, since that’s all a storage driver needs to infer the data unit number to use for each data block in each bio in a request. blk-mq keeps track of the encryption context to be used for all the bios in a request with the request’s rq_crypt_ctx. When the first bio is added to an empty request, blk-mq will program the encryption context of that bio into the request_queue’s keyslot manager, and store the returned keyslot in the request’s rq_crypt_ctx. All the functions to operate on encryption contexts are in blk-crypto.c.“





