India & Pakistan Hit: eXotic Visit Campaign Exposed
ESET reports on a new malicious campaign targeting users in South Asia, initiated in November 2021 and disseminating malware through specialized websites and the Google Play Store.
The infected applications, while providing legitimate functionalities, embed code from the open-source RAT Trojan, XploitSPY. Some apps masquerade as messaging platforms such as Alpha Chat and ChitChat, while others impersonate services for ordering food in Pakistan or the Indian Trilife Hospital. It is reported that approximately 380 victims downloaded these decoy messenger apps and created accounts to use their messaging services.
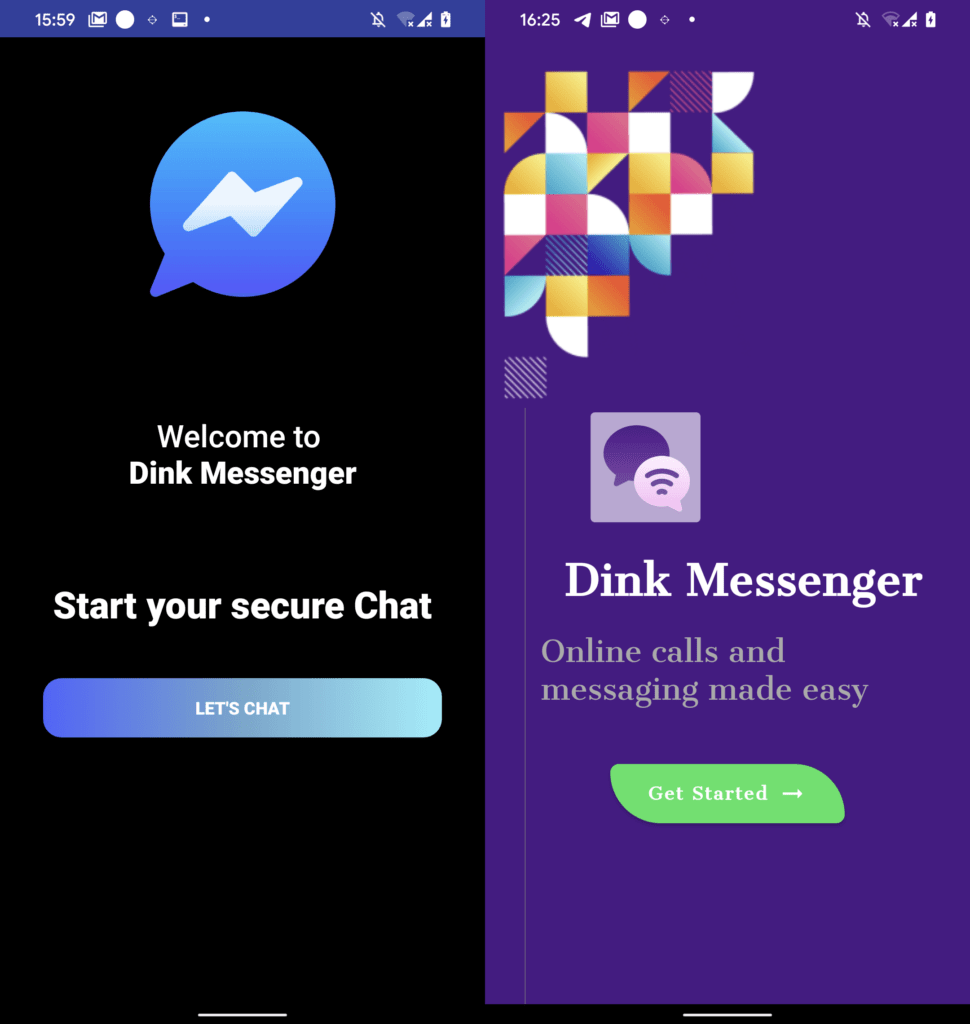
Figure 5. User interface of Dink Messenger downloaded from a dedicated website (left) and Google Play (right)
XploitSPY was uploaded to GitHub in April 2020 by a user named RaoMK and is associated with the Indian cybersecurity firm XploitWizer. The malware is capable of harvesting sensitive data from infected devices, including:
- GPS locations;
- Audio recordings from the microphone;
- Contact lists;
- SMS messages;
- Call logs;
- Clipboard contents.
Additionally, XploitSPY can:
- Download and upload files;
- List installed applications;
- Extract notification details from WhatsApp, Facebook*, Instagram*, and Gmail.
The primary objective of these malicious applications is espionage, presumably with a focus on victims in Pakistan and India. The apps are also designed to enumerate files in several directories associated with screenshots and messengers, including WhatsApp and Telegram.
According to ESET, the perpetrators continually modify their malicious code, adding obfuscation, emulator detection, concealing C2 server addresses, and utilizing native libraries. If emulator use is detected, the application employs a decoy C2 server to evade detection.
The distribution of malicious applications began with websites specifically created for this campaign. These sites provided a link to the APK file hosted on GitHub. Subsequently, distribution moved to the official Google Play Store, where the apps achieved a modest number of installations—up to 45—before the malicious programs were removed following their discovery.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
