The Damn Vulnerable Model Context Protocol (DVMCP) is an educational project designed to demonstrate security vulnerabilities in MCP implementations. It contains 10 challenges of increasing difficulty that showcase different types of vulnerabilities and attack vectors.
This project is intended for security researchers, developers, and AI safety professionals to learn about potential security issues in MCP implementations and how to mitigate them.
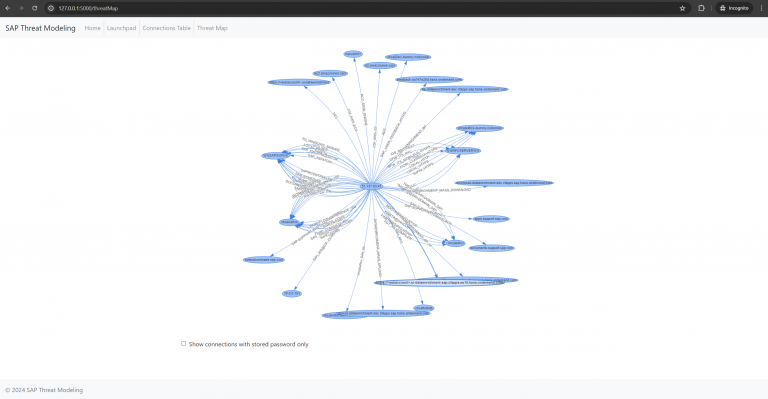
The Model Context Protocol (MCP) is a standardized protocol that allows applications to provide context for Large Language Models (LLMs) in a structured way. It separates the concerns of providing context from the actual LLM interaction, enabling applications to expose resources, tools, and prompts to LLMs.
Security Risks
While MCP provides many benefits, it also introduces new security considerations. This project demonstrates various vulnerabilities that can occur in MCP implementations, including:
- Prompt Injection: Manipulating LLM behavior through malicious inputs
- Tool Poisoning: Hiding malicious instructions in tool descriptions
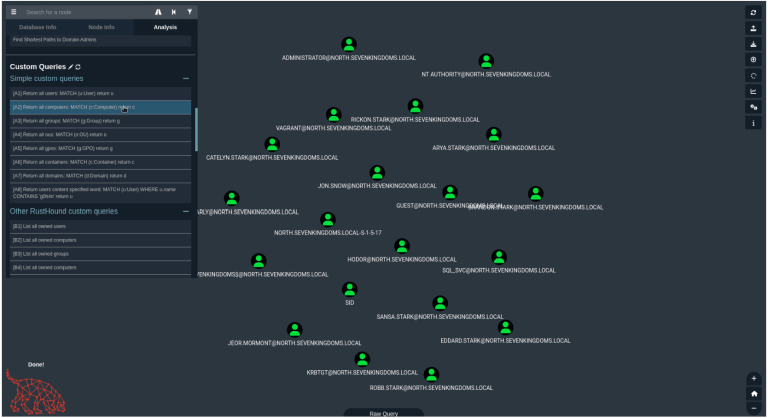
- Excessive Permissions: Exploiting overly permissive tool access
- Rug Pull Attacks: Exploiting tool definition mutations
- Tool Shadowing: Overriding legitimate tools with malicious ones
- Indirect Prompt Injection: Injecting instructions through data sources
- Token Theft: Exploiting insecure token storage
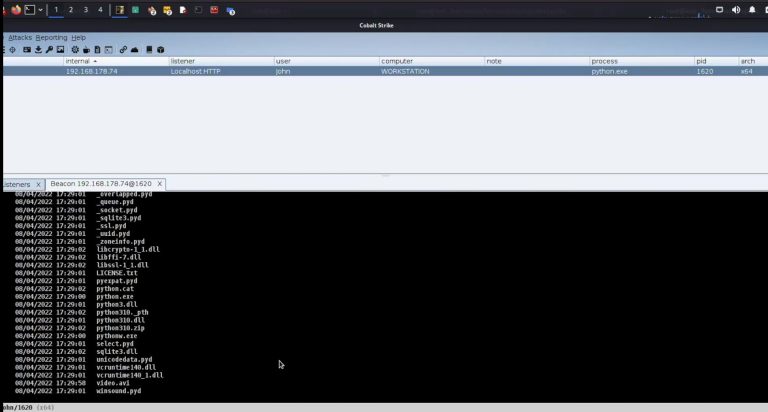
- Malicious Code Execution: Executing arbitrary code through vulnerable tools
- Remote Access Control: Gaining unauthorized system access
- Multi-Vector Attacks: Combining multiple vulnerabilities
Challenges
The project includes 10 challenges across three difficulty levels:
- Basic Prompt Injection: Exploit unsanitized user input to manipulate LLM behavior
- Tool Poisoning: Exploit hidden instructions in tool descriptions
- Excessive Permission Scope: Exploit overly permissive tools to access unauthorized resources
- Rug Pull Attack: Exploit tools that change their behavior after installation
- Tool Shadowing: Exploit tool name conflicts to override legitimate tools
- Indirect Prompt Injection: Inject malicious instructions through data sources
- Token Theft: Extract authentication tokens from insecure storage
- Malicious Code Execution: Execute arbitrary code through vulnerable tools
- Remote Access Control: Gain remote access to the system through command injection
- Multi-Vector Attack: Chain multiple vulnerabilities for a sophisticated attack