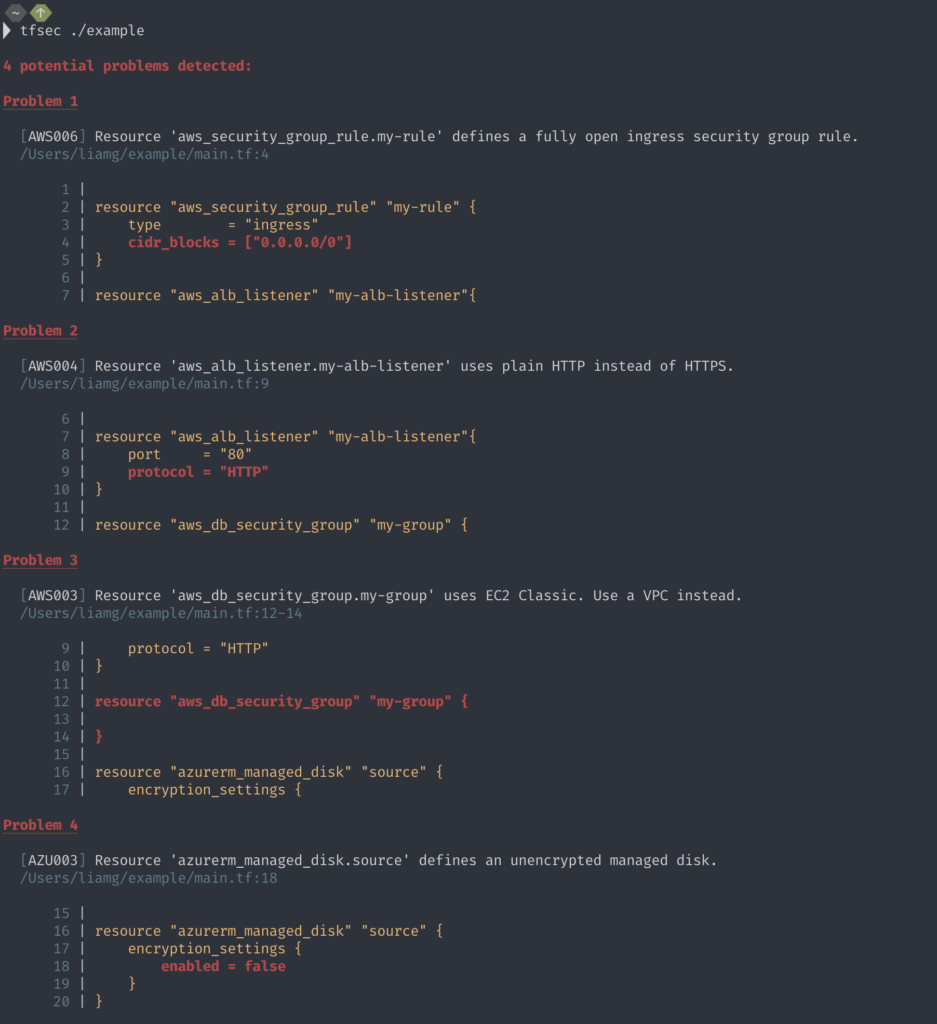
tfsec: Static analysis powered security scanner for your terraform code
tfsec
tfsec uses static analysis of your terraforms templates to spot potential security issues.

Features
- ☁️ Checks for misconfigurations across all major (and some minor) cloud providers
- ⛔ Hundreds of built-in rules
- ? Scans modules (local and remote)
- ➕ Evaluates HCL expressions as well as literal values
- ↪️ Evaluates Terraform functions e.g.
concat() - ? Evaluates relationships between Terraform resources
- ? Compatible with the Terraform CDK
- ? Applies (and embellishes) user-defined Rego policies
- ? Supports multiple output formats: lovely (default), JSON, SARIF, CSV, CheckStyle, JUnit, text, Gif.
- ?️ Configurable (via CLI flags and/or config file)
- ⚡ Very fast, capable of quickly scanning huge repositories
- ? Plugins for popular IDEs available (JetBrains, VSCode and Vim)
- ? Community-driven – come and chat with us on Slack!
Included Checks
Currently, checks are mostly limited to AWS/Azure/GCP resources, but there are also checks which are provider agnostic.
| Code | Provider | Description |
|---|---|---|
| GEN001 | * | Potentially sensitive data stored in “default” value of variable. |
| GEN002 | * | Potentially sensitive data stored in local value. |
| GEN003 | * | Potentially sensitive data stored in block attribute. |
| AWS001 | aws | S3 Bucket has an ACL defined which allows public access. |
| AWS002 | aws | S3 Bucket does not have logging enabled. |
| AWS003 | aws | AWS Classic resource usage. |
| AWS004 | aws | Use of plain HTTP. |
| AWS005 | aws | Load balancer is exposed to the internet. |
| AWS006 | aws | An ingress security group rule allows traffic from /0. |
| AWS007 | aws | An egress security group rule allows traffic to /0. |
| AWS008 | aws | An inline ingress security group rule allows traffic from /0. |
| AWS009 | aws | An inline egress security group rule allows traffic to /0. |
| AWS010 | aws | An outdated SSL policy is in use by a load balancer. |
| AWS011 | aws | A resource is marked as publicly accessible. |
| AWS012 | aws | A resource has a public IP address. |
| AWS013 | aws | Task definition defines sensitive environment variable(s). |
| AWS014 | aws | Launch configuration with unencrypted block device. |
| AWS015 | aws | Unencrypted SQS queue. |
| AWS016 | aws | Unencrypted SNS topic. |
| AWS017 | aws | Unencrypted S3 bucket. |
| AWS018 | aws | Missing description for security group/security group rule. |
| AZU001 | azurerm | An inbound network security rule allows traffic from /0. |
| AZU002 | azurerm | An outbound network security rule allows traffic to /0. |
| AZU003 | azurerm | Unencrypted managed disk. |
| AZU004 | azurerm | Unencrypted data lake store. |
| AZU005 | azurerm | Password authentication in use instead of SSH keys. |
| GCP001 | Unencrypted compute disk. | |
| GCP002 | Unencrypted storage bucket. | |
| GCP003 | An inbound firewall rule allows traffic from /0. |
|
| GCP004 | An outbound firewall rule allows traffic to /0. |
Install && Use
Copyright (c) 2019 Liam Galvin