Specialists from the FBI and CISA have issued a joint warning regarding the intensification of a hacking collective known as Royal Ransomware. According to the agencies, since September 2022, the malefactors have targeted at least 350 companies globally. Earlier in March, a statement was released indicating that the hackers often demanded ransoms exceeding $250 million.
In the spring, experts provided a detailed analysis of the tactics and tools employed by Royal ransomware. This insight enabled many organizations to fortify their corporate systems’ defenses. However, Royal continues to refine its methods, and it remains uncertain whether the current protective measures will prove effective.

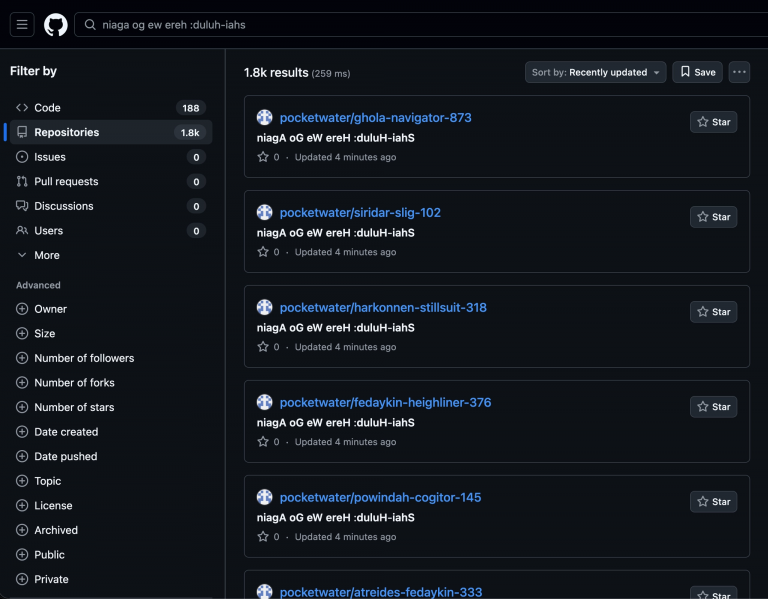
The updated report reveals that in recent months, the ransom demands have surpassed $275 million. The hackers employ a sophisticated attack strategy, stealthily copying valuable data, transferring it to their servers, and demanding money before proceeding to encrypt and publish sensitive files on leak sites. Often, initial access to systems is gained through phishing emails.
Experts report that the criminals are currently testing a new encryptor, BlackSuit, whose code closely resembles older software. This could potentially lead to the emergence of a subgroup under this name, targeting specific types of organizations.
Initially, it was expected that the hackers would completely rebrand Royal ransomware to BlackSuit following the new encryptor’s revelation in May. However, this “rebranding” never transpired. The group continues to actively use Royal, with BlackSuit being applied in limited cases, such as attacks on major businesses.
Royal ransomware previously collaborated with the notorious criminal group Conti. Despite being a relatively recent emergence in 2022, they have swiftly inflicted substantial damage on global business.
Initially, the culprits utilized tools from other groups, particularly the ALPHV/BlackCat ransomware, to disguise their activities. However, they later transitioned to their developments, including the Zeon encryptor, which partially imitated Conti, and later Royal. Recently, this malicious software has been upgraded to target Linux-based devices in attacks focused on VMware ESXi virtual machines.
Support Our Threat Intelligence
If you find our CVE report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee