Phishing Attack Lurks in Nespresso Domain
Cybersecurity researchers from Perception Point recently discovered a vulnerability on the Nespresso coffee machine and capsule manufacturer’s website, which scammers actively exploit to redirect users to malicious sites.
The vulnerability, related to open redirection, allows attackers to redirect users to a malicious site or even embed malicious content directly into a legitimate website.
Attackers can manipulate the URL value, creating links that appear to originate from Nespresso but lead to malicious resources. One such link begins with “t.uk.nespresso.com/r/?id[…]” but ultimately redirects to the perpetrator’s site.
As mentioned, this vulnerability is actively exploited. The attack begins with an email that masquerades as a request for multi-factor authentication from Microsoft, although the sender is unaffiliated with Microsoft. The message is crafted to appear as if it has been forwarded multiple times and looks as though it originates from Microsoft.
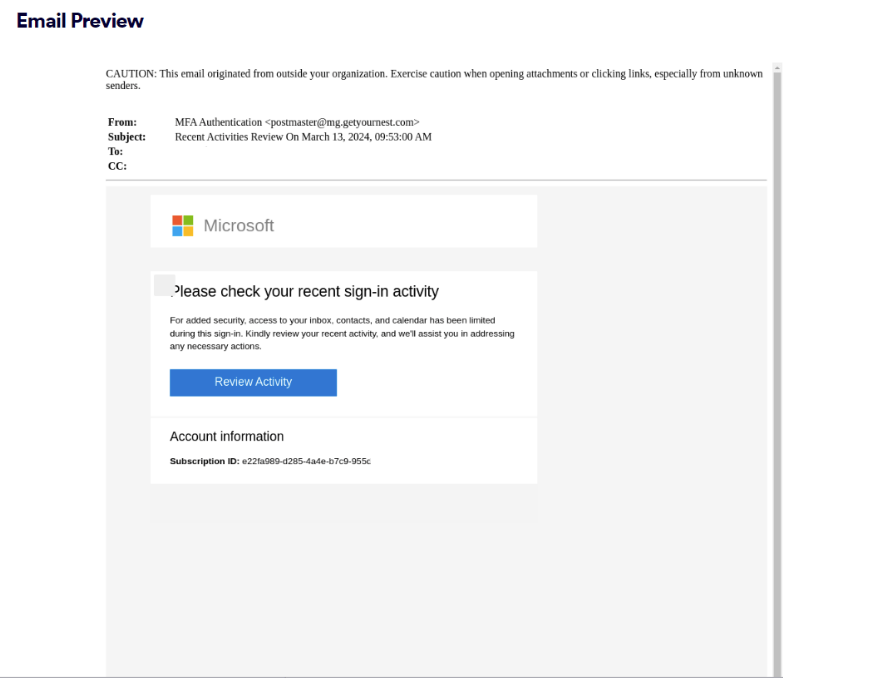
The content of the email urges the recipient to verify their recent login activity. Clicking on the link opens a fake Microsoft login page designed to steal credentials.
The researchers emphasize that using the legitimate, trusted domain of Nespresso allows the scam to bypass mail spam filters and other security measures, as some security systems only check the initial link, without analyzing embedded or hidden links.
Perception Point has observed numerous attacks using the Nespresso domain, originating from various senders. In addition to emails about suspicious activities purportedly from Microsoft, researchers have also recorded similar emails mimicking Bank of America.
As of April 18, the date the researchers published their article, the vulnerability remained unaddressed. The media awaits a response from Nespresso’s press service.
Indeed, this type of attack, exploiting domains with high reputations, is quite common. For instance, in January, we reported that BMW fell victim to attacks with redirections. The exploitation of a flaw on its website led to prolonged targeted phishing and active dissemination of malware.
Users should be wary of clicking on suspicious links in emails, even if the sender seems legitimate. Attackers have long had ways to forge both the sender and the links within the email, as demonstrated by the described open redirection flaw.





