Orca Security Exposes Sys:All: A GKE Flaw Putting 250,000 Clusters at Risk
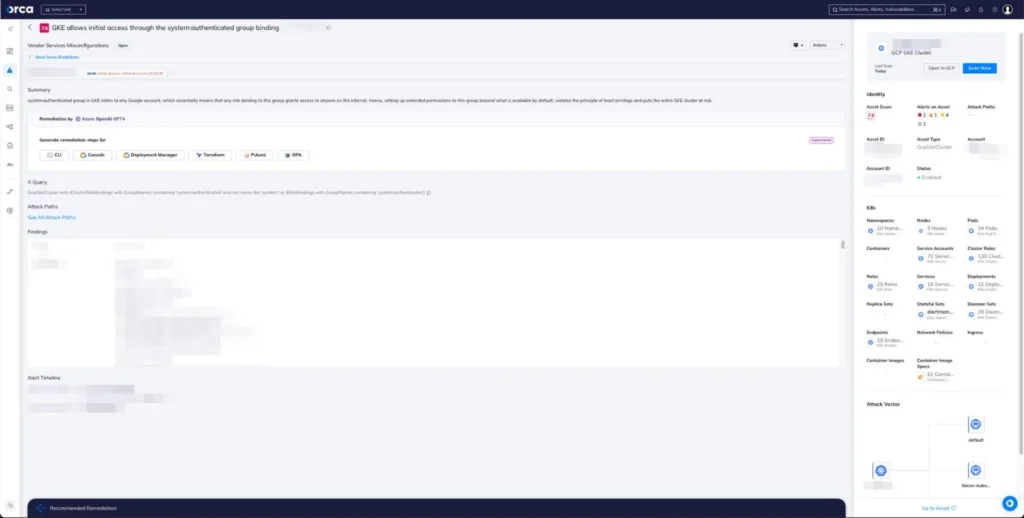
The cybersecurity firm Orca Security has identified a vulnerability in Google Kubernetes Engine (GKE) that enables individuals with a Google account to gain control over Kubernetes clusters. This issue has been codenamed Sys:All. It is estimated that approximately 250,000 active GKE clusters are susceptible to this vulnerability.
According to Orca Security’s report, the crux of the problem lies in a widespread misunderstanding concerning the system:authenticated group in GKE. This special group encompasses all authenticated entities, including users and service accounts. Many assume that the group only includes verified users, whereas it comprises any Google accounts. This misunderstanding can have grave implications, as administrators may inadvertently grant overly broad permissions to this group.
The potential danger escalates with external malicious actors who could use their Google OAuth 2.0 token to take control of a cluster and subsequently employ it for various malicious purposes, including cryptocurrency mining, Denial of Service (DoS) attacks, and theft of confidential data. Moreover, such an approach leaves no traceable evidence that could be linked back to a specific Gmail or Google Workspace account.
At risk are various sensitive data, including JWT tokens, GCP API keys, AWS keys, Google OAuth credentials, private keys, and access to container registries, which could lead to the injection of malicious code into container images.
Google has already taken measures to rectify the flaw, prohibiting the binding of the system:authenticated group to the cluster-admin role in GKE versions 1.28 and later. The company also advises users not to bind the system:authenticated group to any RBAC (role-based access control) roles and to check whether their clusters are associated with the group.
Additionally, Google has integrated detection rules into Event Threat Detection and preventative rules into Policy Controller. All GKE users with bindings to these groups have been sent email notifications urging them to review their configurations.
Orca researchers caution that despite Google’s enhancements, numerous other roles and permissions can still be assigned to the system:authenticated group. Organizations are advised to ensure that the group does not possess excessive privileges to avoid potential threats.
Support Our Threat Intelligence
If you find our technology report and cybersecurity news helpful, consider supporting our work.
 Buy Me a Coffee
Buy Me a Coffee
