Microsoft confirms that Windows 10 v1809 will accidentally disable the local Administrator account
The latest official blog of Microsoft reminds users that if they try to upgrade from the old version to Windows 10 Version 1809, the administrator account may be disabled.
For example, if the administrator account is enabled on the Windows 10 April Update, the administrator rights account will be disabled and cannot be logged in after upgrading the new version.
This issue primarily affects users who use the local Administrator account. If the user is using a Microsoft online account, then this will not be affected.
And coming to the current article, the issue happens in below cases where
- The built-in administrator account is active
- Other account present that has administrator rights.
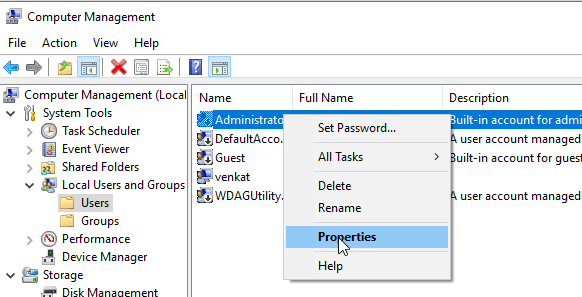
In addition, you can use the account with other administrator privileges to log in to the system and you can enable the Administrator account again. Microsoft will fix this problem this month.
Via: techdows