LogHunter: Opsec tool for finding user sessions by analyzing event log files through RPC
LogHunter
Opsec tool for finding user sessions by analyzing event log files through RPC (MS-EVEN).
I was once doing a very complex project where there were over 1000 hosts in the infrastructure. I needed to detect the user session. Running Invoke-UserHunter would have been a huge mistake. That’s when I came up with the idea that we could extract all the information we needed from Event Logs. That’s how the LogHunter tool came into being. The tool can extract the following events via MS-EVEN protocol: 4624: “An account was successfully logged on.”, 4768: “A Kerberos authentication ticket (TGT) was requested.”, 4672: “Special privileges assigned to new logon.”, 4769: “A Kerberos service ticket (TGS) was requested.”.
These events will give us information about which computer the target user is on. Then hijack that computer and take control of the user.
Install
git clone https://github.com/CICADA8-Research/LogHunter.git
pip install impacket
Use
To use the tool, all you need to do is pass credentials as you would to a regular impacket tool:
python LogHunter.py OFFICE/Administrator:lolkekcheb123!@dc01.office.pwn

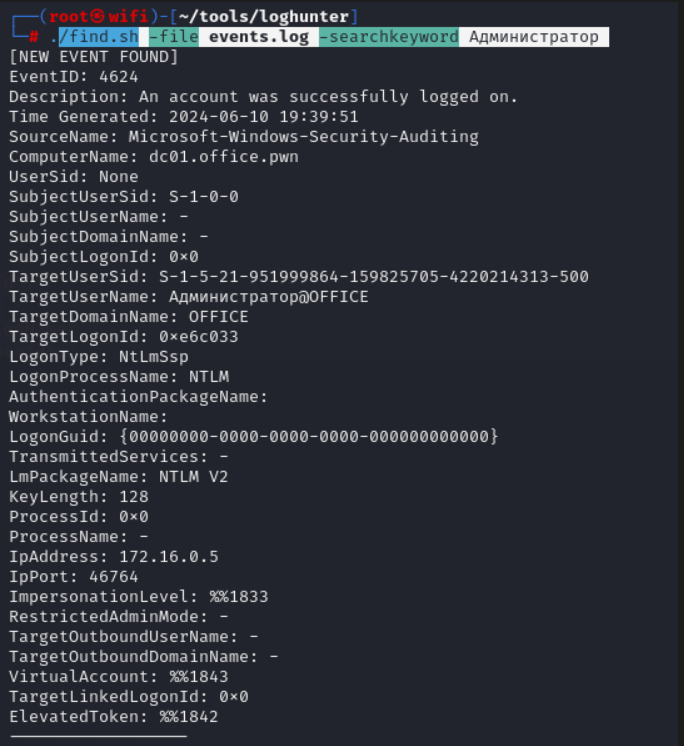
After that, the tool will start receiving events from the target computer (in this case, from dc01.office.pwn), writing them to the events.log file (can be overridden with the -outfile parameter). You can then search for the file using find.sh. You can search by user name, by EventID, or by computer name – whatever you prefer.
./find.sh -file events.log -searchkeyword Administrator