GTPDOOR Scan
A multithreaded network scanner to scan for hosts infected with the GTPDOOR malware. Technical writeup here.
Three detection methods are supported:
- ACK scan (detects GTPDOOR v2)
- TCP connect scan (detects GTPDOOR v2)
- GTP-C GTPDOOR message type 0x6 (detects GTPDOOR v1 + v2) if default hardcoded key has not been changed
Note that for 1+2, the GTPDOOR implant must have ACLs configured for its TCP RST/ACK beacon to respond. Given these conditions, it cannot be guaranteed that GTPDOOR will be detected alone from active network scanning.
Additional information
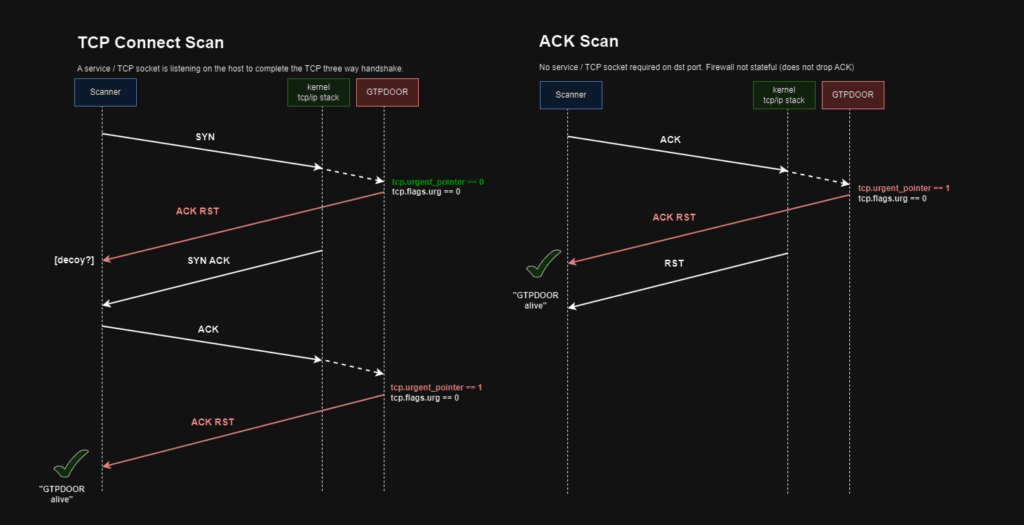
GTPDOOR version 2 will respond with a TCP ACK/RST message with the URG flag not set but the urgent TCP field set to 0x01 on receiving a TCP ACK either from a TCP three way handshake (--connect parameter) or a single ACK (--ACK parameter) ingress ACK packet.
GTPDOOR will also fire off a TCP ACK/RST from an incoming TCP SYN packet, but the urgent field will be set to zero. This condition is not considered a unique GTPDOOR beacon, and hence is ignored.
GTPDOOR version 1 does not support TCP probe/beacons. The detection method implemented here is to send a GTPDOOR GTP-C message with the message type of 0x06 which is a GTPDOOR ACL query message (--gtp parameter). The default auth/encryption key is used.
Use
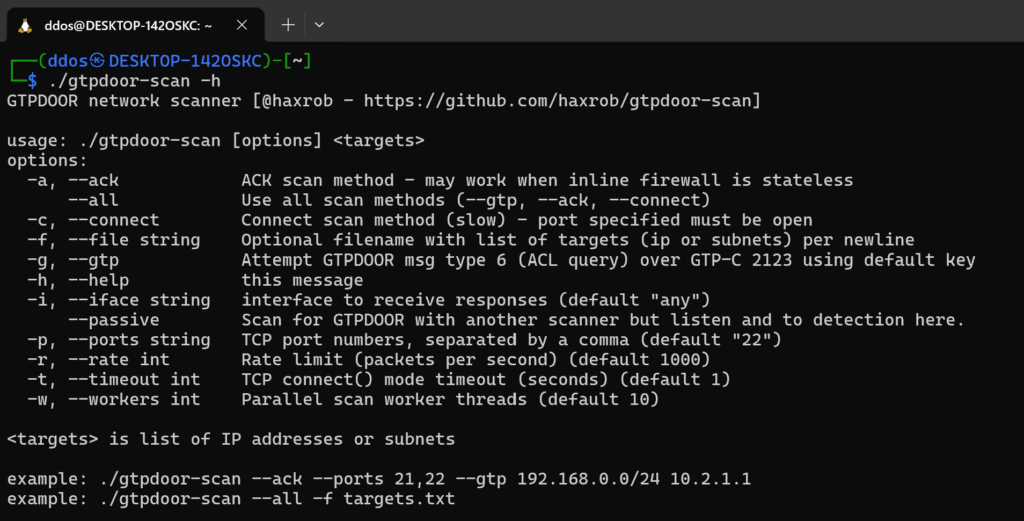
Using --all will initiate all three scan modes (--gtp,--connect, --ack). A note on the TCP connect scan, a target’s TCP port must be responding. For the ACK mode, any arbitrary port can be chosen. It is assumed that that GTPDOOR is designed to support beaconing when the infected host is behind a stateful firewall with at least one TCP port open by using a connect scan, or a stateless firewall with an ACK scan.
NOTE: The GTPDOOR message scan --gtp only attempts to invoke GTPDOOR’s ACL query message type and not the remote code execution message in order to avoid arbitrary code execution. The contents of the GTP message response is discarded. That said, if you do not have permission to scan assets with gtpdoor-scan, you may want to be careful. Security researchers wishing to be cautious may want to consider avoiding the --gtp flag.
External network scanner support
gtpdoor-scan can also be used alongside an external network scanner such as nmap or masscan by using the --passive switch. For example, nmap’s TCP ACK Scan could be run while gtpdoor-scan is running on the same host in passive mode. While nmap may report the port as unfiltered, gtpdoor-scan will report that it received a possible beacon, indicating that GTPDOOR may have been running on the remote host.
$ gtpdoor-scan --passive &
$ nmap -sA <target>
The x86-64 / version 1 sample does not support TCP beaconing, so an external scanner will not be able to detect it.
Download
Copyright (c) 2024 HaxRob