A software engineer from SkySafe, Mark Newlin, discovered a perilous vulnerability in Bluetooth, that existed since around 2012. This flaw enables malefactors to connect to Apple, Android, and Linux devices without authentication and execute arbitrary commands. The flaw, designated as CVE-2023-45866, does not require specialized equipment for exploitation, rendering it particularly dangerous.
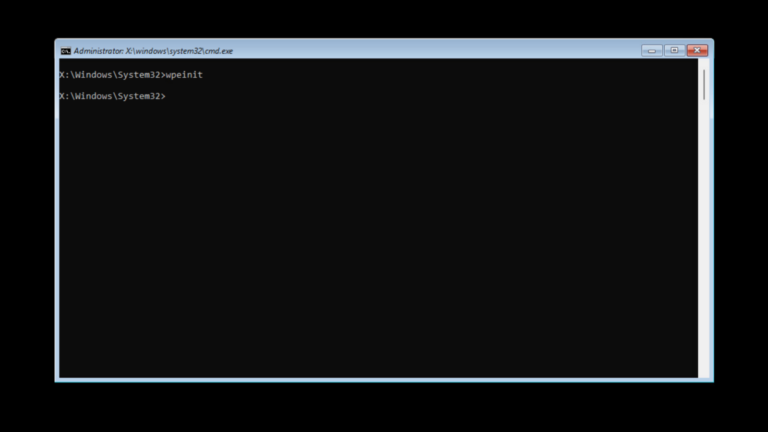
According to the researcher, such an attack can be executed using a standard Bluetooth adapter on a computer running the Linux operating system.

Newlin’s post on GitHub states: “The vulnerabilities work by tricking the Bluetooth host state-machine into pairing with a fake keyboard without user-confirmation. The underlying unauthenticated pairing mechanism is defined in the Bluetooth specification, and implementation-specific bugs expose it to the attacker.”
Newlin plans to present the vulnerability details and a demonstration code at an upcoming conference but intends to wait until the issue is resolved. He has already reported it to Apple, Google, Canonical, and the Bluetooth Special Interest Group (SIG).
This is not the first such bug discovered by Newlin. In 2016, he identified other defects in Bluetooth affecting wireless mice and keyboards from 17 manufacturers.
Google states that fixes for Android versions 11,12, 13, and 14 are available to original equipment manufacturers, with all supported Pixel devices set to receive the update in December. However, there is no solution yet for Android 4.2.2 – 10.
In Linux, the issue was resolved in 2020, but most distributions, including Ubuntu, Debian, and others, have left the update disabled by default.
The CVE-2023-45866 vulnerability also affects macOS and iOS. The threat is particularly relevant when Bluetooth is activated and a Magic Keyboard is connected to the device. Apple has acknowledged the problem but has not yet shared plans for its resolution.