Brazilian banking institutions have become the target of a new campaign disseminating a specialized variant of the AllaKore remote access trojan (RAT) for Windows, named AllaSenha. This RAT is designed to steal credentials necessary for accessing bank accounts and utilizes the Azure cloud platform as its command-and-control (C2) infrastructure.
In their technical analysis, cybersecurity firm HarfangLab detailed the campaign. The attack targets banks such as Banco do Brasil, Bradesco, Banco Safra, Caixa Econômica Federal, Itaú Unibanco, Sicoob, and Sicredi. It is believed that the perpetrators use phishing emails with malicious links for initial access.
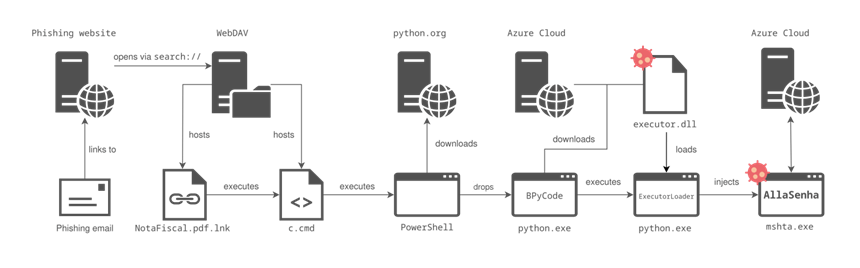
The infection chain generally follows this sequence:
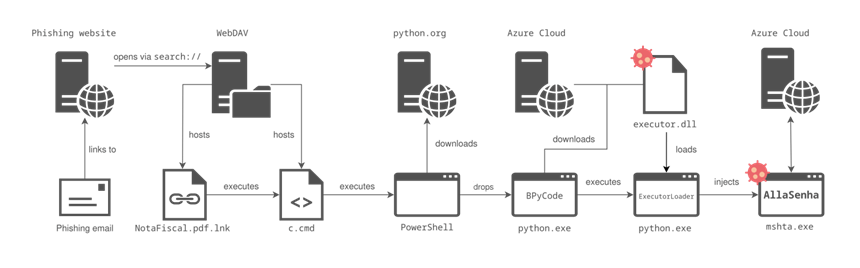
1. The attack begins with the execution of a Windows LNK shortcut disguised as a PDF document hosted on a WebDAV server.
2. The shortcut opens a Windows command shell, displays a decoy PDF document, and downloads a BAT file named “c.cmd.”
3. The BAT file executes a PowerShell command that downloads a Python binary from the official site (python.org) and runs a BPyCode script.
4. The BPyCode script downloads and executes a dynamic link library (executor.dll).
5. The DLL is executed in memory and injects the AllaSenha trojan into the legitimate process “mshta.exe.”
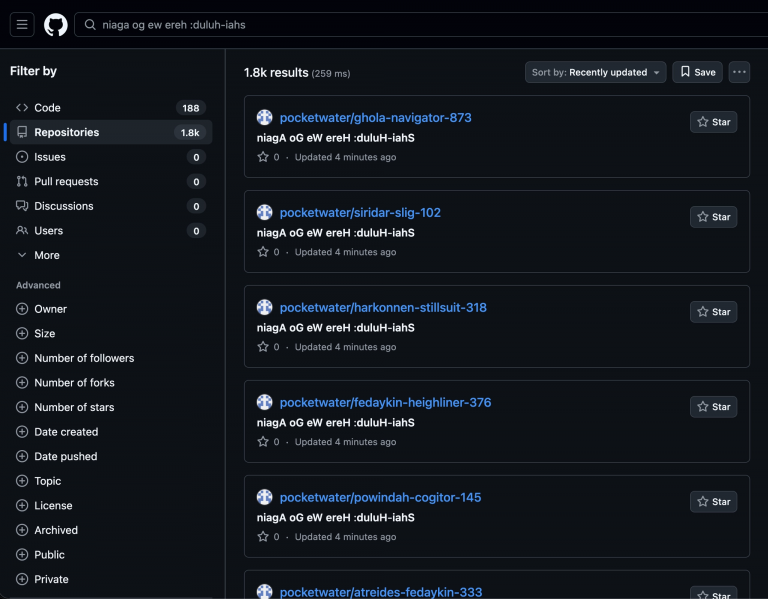
It is noteworthy that the DLL is extracted from one of the domain names generated using a domain generation algorithm (DGA). The generated host names correspond to those associated with the Microsoft Azure Functions service, a serverless infrastructure that allows operators to easily deploy and manage intermediary infrastructure.
In addition to stealing online banking credentials from web browsers, AllaSenha can display overlay windows to capture two-factor authentication (2FA) codes and even trick victims into scanning a QR code to approve fraudulent transactions initiated by the attackers.
HarfangLab also reported that all AllaSenha samples use Access_PC_Client_dll.dll as the original file name. This name is found in the KL Gorki project—a banking malware that seemingly combines components of AllaKore and ServerSocket.
Further analysis of the source code linked to the initial LNK file and AllaSenha samples indicated that a Portuguese-speaking user with the nickname bert1m might be involved in the malware’s development. However, there is no evidence yet that he is actively managing the tools.
Cybercriminals operating in Latin America are often particularly prolific in creating such threats. While their targets are primarily residents of Latin America, they frequently compromise computers belonging to companies worldwide but managed by employees or subsidiaries in Brazil.