Recently, hackers have increasingly employed DNS tunneling to monitor when victims open phishing emails and click on malicious links, as well as to scan networks for vulnerabilities.
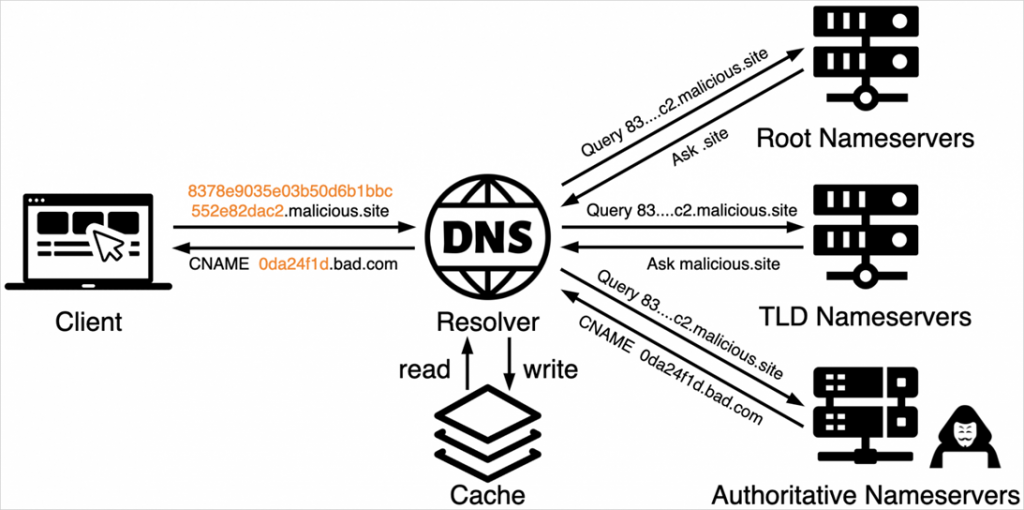
DNS tunneling involves encoding data or commands that are sent and received through DNS queries, transforming DNS—a critical component of network communication—into a covert data transmission channel.
Attackers encode data using methods such as Base16 or Base64, or employ proprietary text encoding algorithms, so that the data can be retrieved through DNS record queries such as TXT, MX, CNAME, and Address.
DNS tunneling is frequently used by hackers to bypass firewalls and filters in operations involving C2 infrastructure and VPN networks.
The Unit 42 research team from Palo Alto Networks recently uncovered additional instances of DNS tunneling being utilized in malicious campaigns aimed at tracking victims and scanning networks.
The first campaign, dubbed “TrkCdn,” focuses on tracking victims’ interactions with phishing emails. Hackers embed content in an email that, when opened, makes a DNS request to subdomains controlled by the attackers.
These subdomains return a DNS response that directs to a server controlled by the attackers, which then delivers malicious content such as advertisements, spam, or phishing materials.
The Unit 42 report also describes a campaign using DNS tunneling for tracking spam message delivery, named “SpamTracker.” This campaign is similar to “TrkCdn,” but is aimed at monitoring spam delivery.
Another campaign identified by analysts, called “SecShow,” uses DNS tunneling to scan network infrastructures. Hackers embed IP addresses and timestamps in DNS queries for subsequent mapping of network configurations and identification of potential vulnerabilities that could be exploited for intrusion, data theft, or denial-of-service attacks.
Hackers choose DNS tunneling over more traditional methods to circumvent security measures, avoid detection, and maintain operational flexibility.
Unit 42 researchers recommend that organizations implement DNS monitoring and analysis tools to track and analyze logs for unusual traffic patterns and anomalies, such as atypical or high-volume requests. Experts also advise limiting the use of DNS resolvers in the network to handle only necessary queries, thereby reducing the likelihood of DNS tunneling abuse.