Category: Network Defense
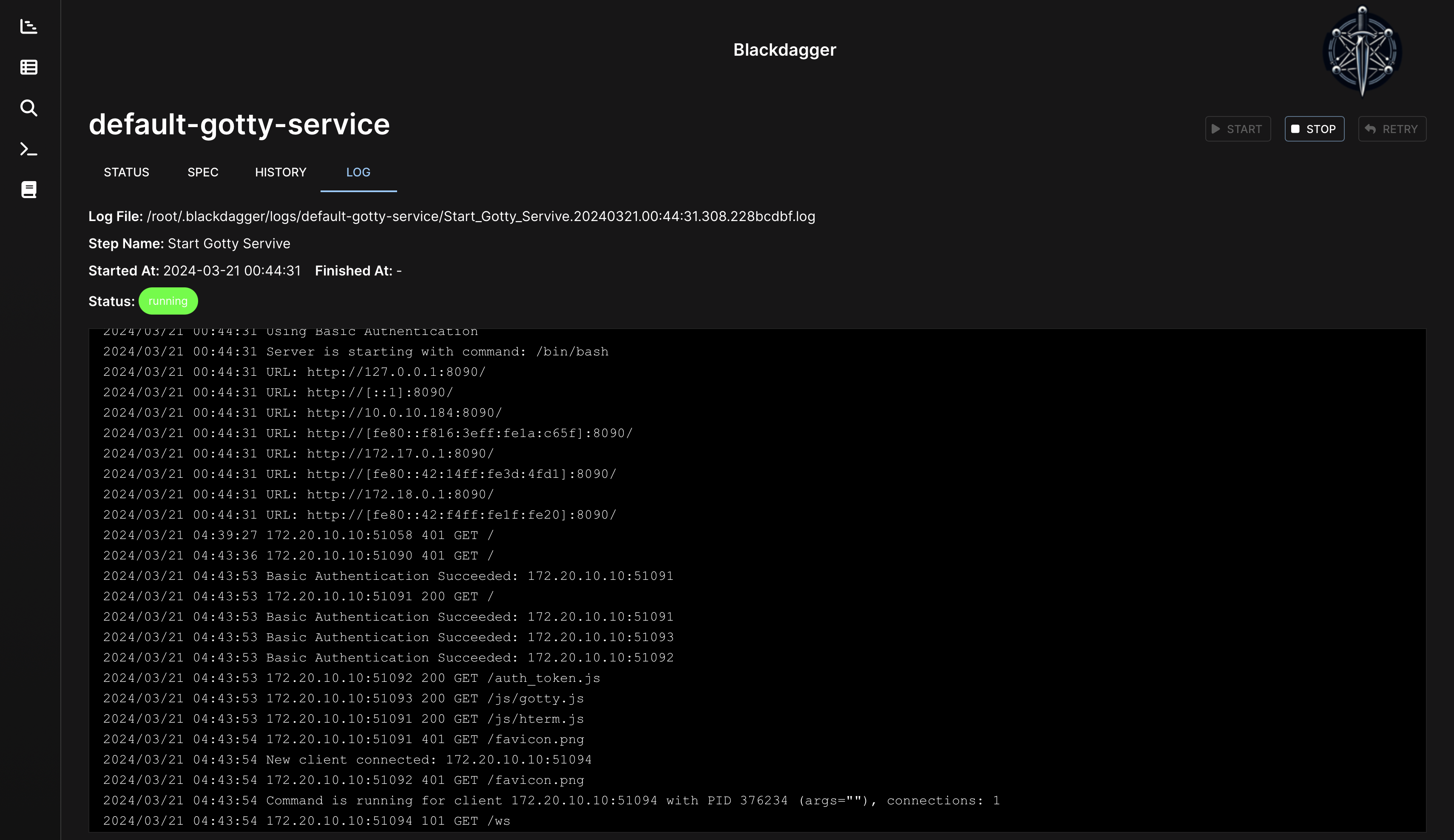
Blackdagger Blackdagger represents a significant advancement in automation technology, offering a comprehensive solution for orchestrating complex workflows in DevOps, DevSecOps, MLOps, MLSecOps, and Continuous Automated Red Teaming (CART) environments. At its core, Blackdagger simplifies...
Netis Packet Agent Netis Packet Agent is an open-source project to deal with such a situation: it captures packets on Machine A but has to use them on Machine B. This case is very common when...
Miteru Miteru is an experimental phishing kit detection tool. How it works It collects phishing suspicious URLs from the following feeds: urlscan.io certstream-suspicious feed OpenPhish feed via urlscan.io PhishTank feed via urlscan.io It checks...
Cloud Console Cartographer Released at Black Hat Asia on April 18, 2024, Cloud Console Cartographer is a framework for condensing groupings of cloud events (e.g. CloudTrail logs) and mapping them to the original user...
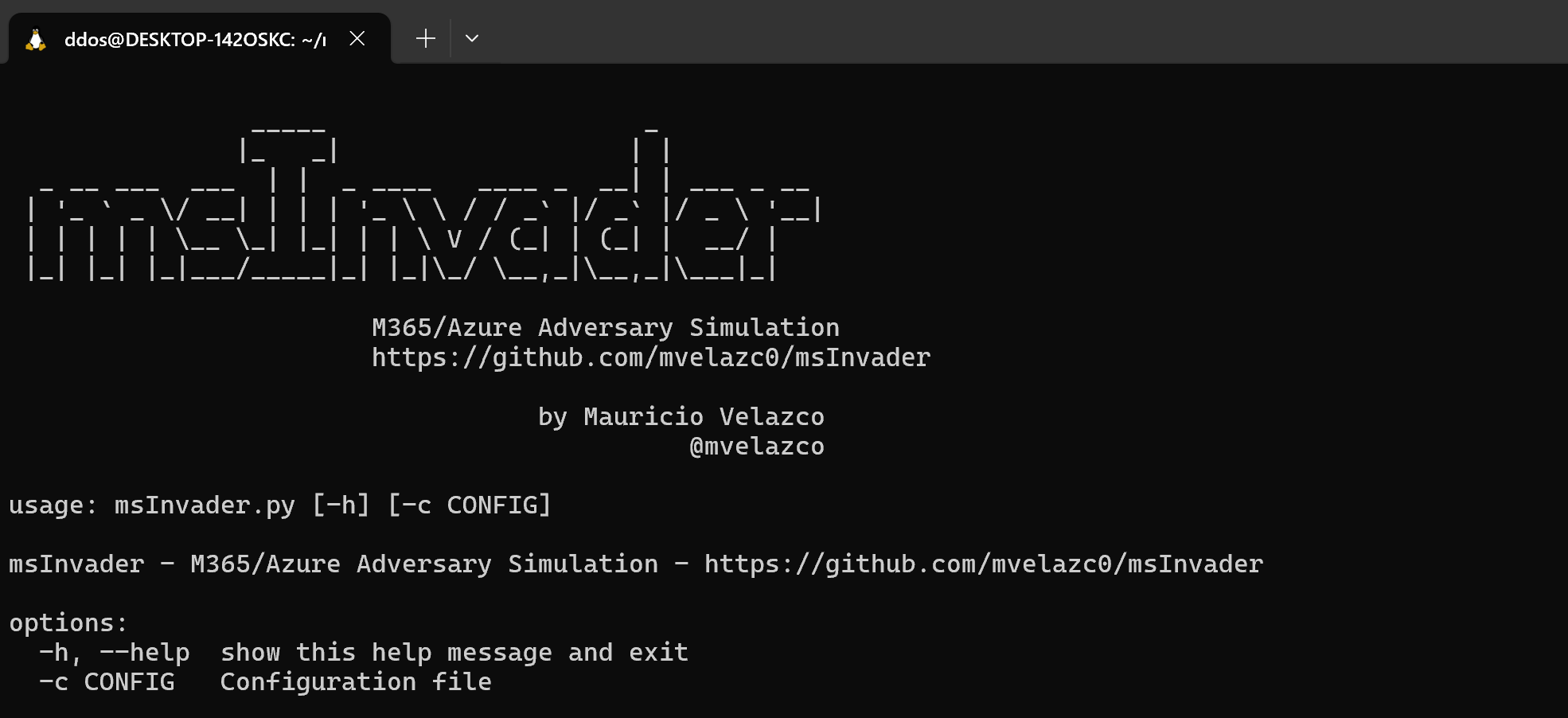
msInvader msInvader is an adversary simulation tool built for blue teams, designed to simulate adversary techniques within M365 and Azure environments. Its purpose is to generate attack telemetry that aids teams in building, testing,...
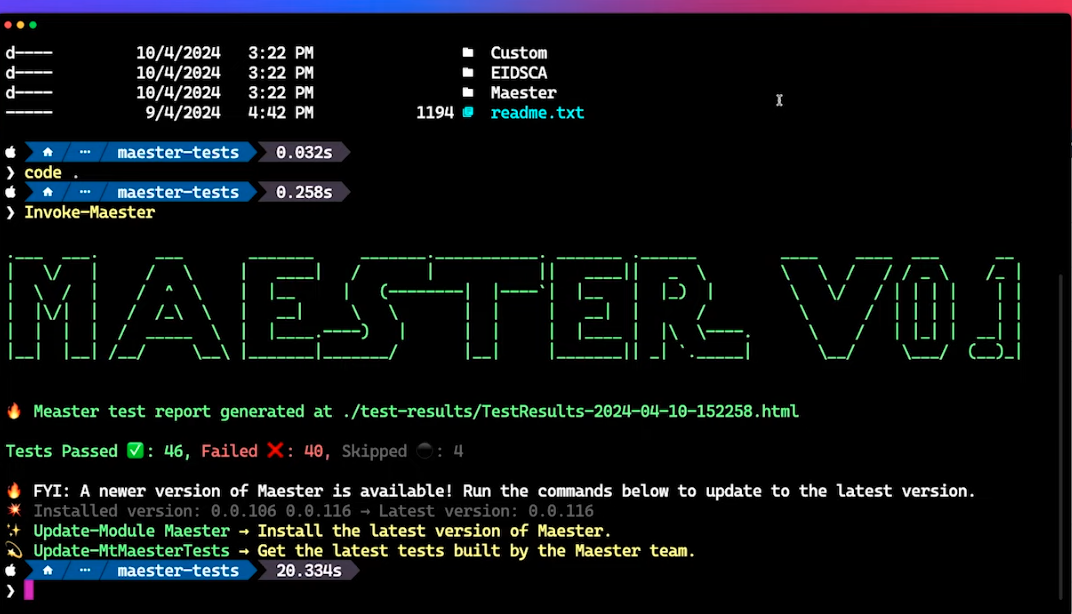
Maester Monitor your Microsoft 365 tenant’s security configuration using Maester! Maester is an open source PowerShell-based test automation framework designed to help you monitor and maintain the security configuration of your Microsoft 365 environment. Why Maester?...
simplewall A simple tool to configure Windows Filtering Platform (WFP) which can configure network activity on your computer. The lightweight application is less than a megabyte, and it is compatible with Windows Vista and...
VECTR is a tool that facilitates tracking of your red and blue team testing activities to measure detection and prevention capabilities across different attack scenarios. VECTR provides the ability to create assessment groups, which...
DICOMHawk DICOMHawk is a powerful and efficient honeypot for DICOM servers, designed to attract and log unauthorized access attempts and interactions. Built using Flask and pynetdicom, DICOMHawk offers a streamlined web interface for monitoring...
Paladin Cloud Paladin Cloud is an extensible, Security-as-Code (SaC) platform designed to help developers and security teams reduce risks in their cloud environments. It functions as a policy management plane across multi-cloud and enterprise...
domain-protect scan Amazon Route53 across an AWS Organization for domain records vulnerable to takeover scan Cloudflare for vulnerable DNS records take over vulnerable subdomains yourself before attackers and bug bounty researchers automatically create known issues in Bugcrowd or HackerOne...
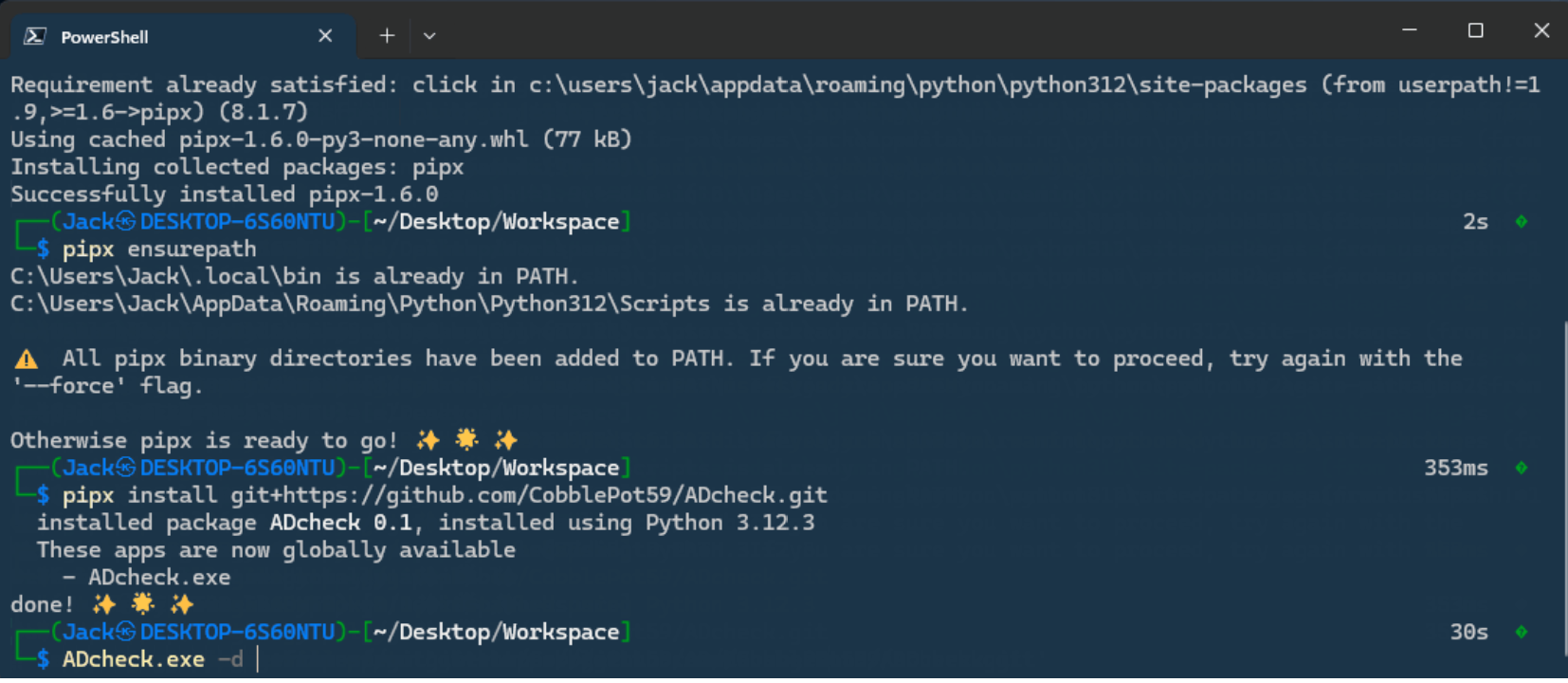
ADcheck Assess the security of your Active Directory with few or all privileges. This tool offers functionalities similar to PingCastle, ORADAD, or even PurpleKnight (with some bonuses). ADcheck is developed in pure Python to bypass operating system...
FalconHound FalconHound is a blue team multi-tool. It allows you to utilize and enhance the power of BloodHound in a more automated fashion. It is designed to be used in conjunction with an SIEM...
Gatekeeper What is Gatekeeper? Gatekeeper is the first open-source DoS protection system. It is designed to scale to any peak bandwidth, so it can withstand DoS attacks both today and tomorrow. In spite of...
Venator – Threat Detection Platform A flexible detection system that simplifies rule management and deployment with K8s CronJob and Helm. Venator is optimized for Kubernetes deployment but is flexible enough to run standalone or...
Network Flight Recorder NFR is a lightweight application which processes network traffic using the AlphaSOC Analytics Engine. NFR can monitor log files on disk (e.g. Microsoft DNS debug logs, Bro IDS logs) or run as a network...