Category: Vulnerability Assessment
TInjA – the Template INJection Analyzer TInjA is a CLI tool for testing web pages for template injection vulnerabilities. It supports 44 of the most relevant template engines (as of September 2023) for eight different programming languages. Features...
YATAS – Yet Another Testing & Auditing Solution The goal of YATAS is to help you create a secure AWS environment without too much hassle. It won’t check for all best practices but only...
GPT_Vuln-analyzer This is a Proof Of Concept application that demonstrates how AI can be used to generate accurate results for vulnerability analysis and also allows further utilization of the already super useful ChatGPT made...
JSpector JSpector is a Burp Suite extension that passively crawls JavaScript files and automatically creates issues with URLs and endpoints found on the JS files. Prerequisites Before installing JSpector, you need to have Jython...
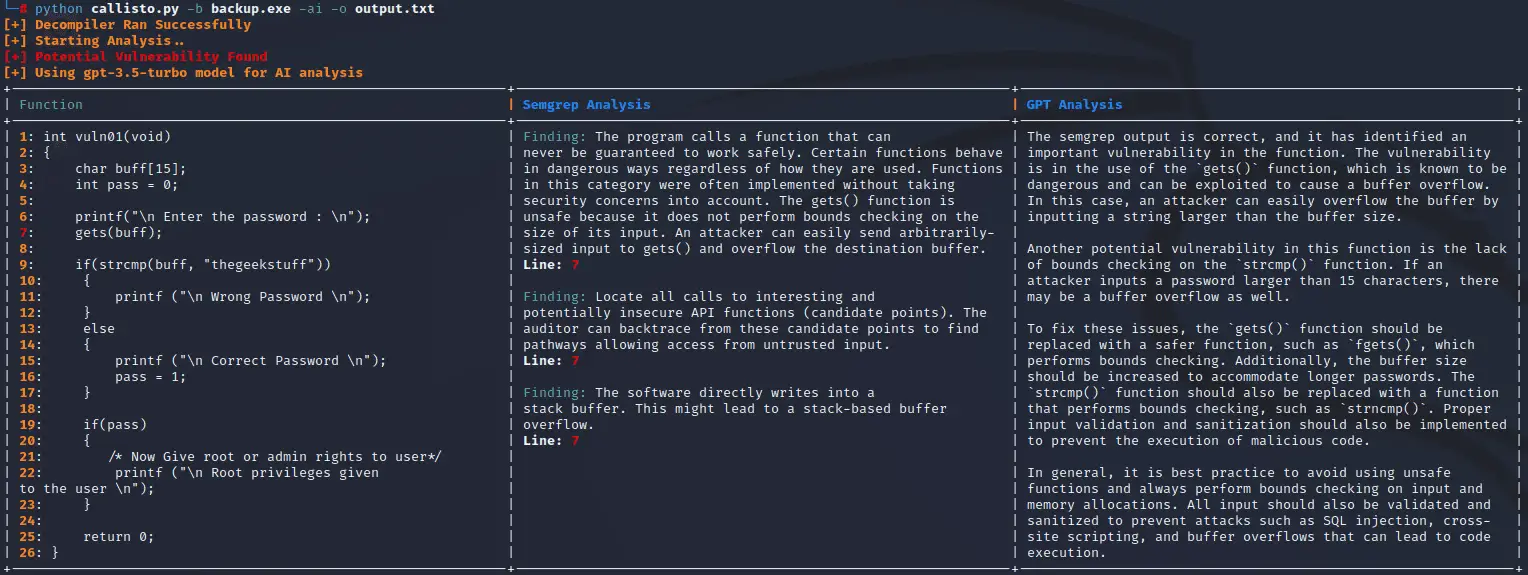
Callisto An Intelligent Automated Binary Vulnerability Analysis Tool Callisto is an intelligent automated binary vulnerability analysis tool. Its purpose is to autonomously decompile a provided binary and iterate through the pseudo code output looking...
GCP Scanner This is a GCP resource scanner that can help determine what level of access certain credentials possess on GCP. The scanner is designed to help security engineers evaluate the impact of a...
What is Akto? Akto is an instant, open source API security platform that takes only 60 secs to get started. Akto is used by security teams to maintain a continuous inventory of APIs, test...
Sirius Scan Sirius is the first truly open-source general purpose vulnerability scanner. Today, the information security community remains the best and most expedient source for cybersecurity intelligence. The community itself regularly outperforms commercial vendors....
DeepSecrets – a better tool for secret scanning Yet another tool – why? Existing tools don’t really “understand” code. Instead, they mostly parse texts. DeepSecrets expands classic regex-search approaches with semantic analysis, dangerous variable...
IOCTLance Presented at CODE BLUE 2023, this project titled Enhanced Vulnerability Hunting in WDM Drivers with Symbolic Execution and Taint Analysis introduces IOCTLance, a tool that enhances its capacity to detect various vulnerability types in Windows Driver...
Sucosh Scanny “Sucosh” is an automated Source Code vulnerability scanner(SAST) and assessment framework for Python(Flask-Django) & NodeJs capable of performing code review in Web Application Developing or Source Code Analysis processes. It can detect...
CLZero A project for fuzzing HTTP/1.1 CL.0 Request Smuggling Attack Vectors. Inspired by the tool Smuggler all attack gadgets adapted from Smuggler and https://portswigger.net/research/how-to-turn-security-research-into-profit CL.0 Identification method The first request will be the “base” request. This is...
AtlasReaper AtlasReaper is a command-line tool developed for offensive security purposes, primarily focused on a reconnaissance of Confluence and Jira. It also provides various features that can be helpful for tasks such as credential...
WebCopilot WebCopilot is an automation tool designed to enumerate subdomains of the target and detect vulnerabilities using different open-source tools. The script first enumerates all the subdomains of the given target domain using assetfinder,...
What is BinAbsInspector? BinAbsInspector (Binary Abstract Inspector) is a static analyzer for automated reverse engineering and scanning vulnerabilities in binaries, which is a long-term research project incubated at Keenlab. It is based on abstract interpretation...
shortscan Shortscan is designed to quickly determine which files with short filenames exist on an IIS webserver. Once a short filename has been identified the tool will try to automatically identify the full filename....