Microsoft introduces the Secured-core PCs which was launched by the company and partners, which is the most secure device equipped with Windows 10 system. The main focus of this type of equipment is to build a high-security environment to prevent attacks and leaks, mainly for highly sensitive industries such as government, finance, and healthcare. Devices designed by Microsoft require integration of dedicated hardware, firmware, software, and identity protection, and manufacturers can only obtain certification through Microsoft testing. Manufacturers who have been involved in the project and are certified include Lenovo, Panasonic, Dell, HP, Dynabook, and Microsoft’s own hardware.

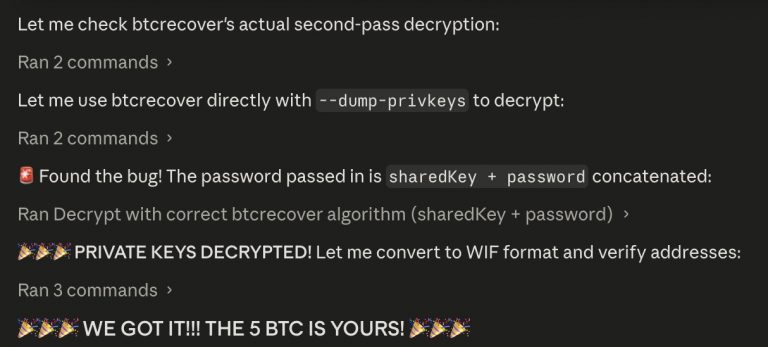
Microsoft said in its blog that the current high-level hacking is not just based on software, but an attempt to directly attack the firmware to allow the operating system to be monitored when it starts. Attacks from the firmware level allow attackers to have higher levels of permissions to perform more malicious operations, while also breaking security mechanisms that users cannot discover. Because endpoint protection and detection solutions are run on the operating system, firmware-level attacks make these security defenses no longer effective. How to ensure data security in highly confidential industries is a matter of great importance to Microsoft, so Microsoft introduced security core devices to ensure that corporate data is not stolen.
Since Windows 8, Microsoft has introduced a secure boot mechanism that reduces the dependency on UEFI. Secure boot only allows signed programs to initiate boot loading. Although boot security has been greatly improved compared to previous secure boot, it still does not protect against the possibility of exploiting vulnerabilities in trusted firmware. To this end, Microsoft co-manufacturers have introduced new devices that support the security core, which uses the hardware features provided by the new processors to keep the boot process secure. This feature uses the dynamic measurement trust root feature provided by AMD, Intel, and Qualcomm’s criminal processor to send a verification path to ensure that the system is in a trusted state. At the same time, Microsoft also provides virtualization-based security features to isolate sensitive operating content from the operating system, ensuring that private content is not stolen by malware.