VMware Products Security Vulnerability Alert
Recently, VMware released a risk notification [1, 2] for multiple vulnerabilities in desktop virtualization products. This security update is aimed at multiple virtualization products under VMware, and local attackers can trigger vulnerabilities with low user privileges.
Vulnerability Details
- CVE-2020-3960 VMware ESXi, Workstation and Fusion out-of-bounds read vulnerability
A malicious actor with local non-administrative access to a virtual machine may be able to read privileged information contained in memory.
- CVE-2020-3957 Service opener – Time-of-check Time-of-use (TOCTOU) issueSuccessful exploitation of this issue may allow attackers with normal user privileges to escalate their privileges to root on the system where Fusion, VMRC, and Horizon Client are installed.
- CVE-2020-3958 Denial-of-service vulnerability in Shader functionality
Successful exploitation of this issue may allow attackers with non-administrative access to a virtual machine to crash the virtual machine’s vmx process leading to a denial of service condition.
- CVE-2020-3959 Memory leak vulnerability in VMCI module
A malicious actor with local non-administrative access to a virtual machine may be able to crash the virtual machine’s vmx process leading to a partial denial of service.
Affected version
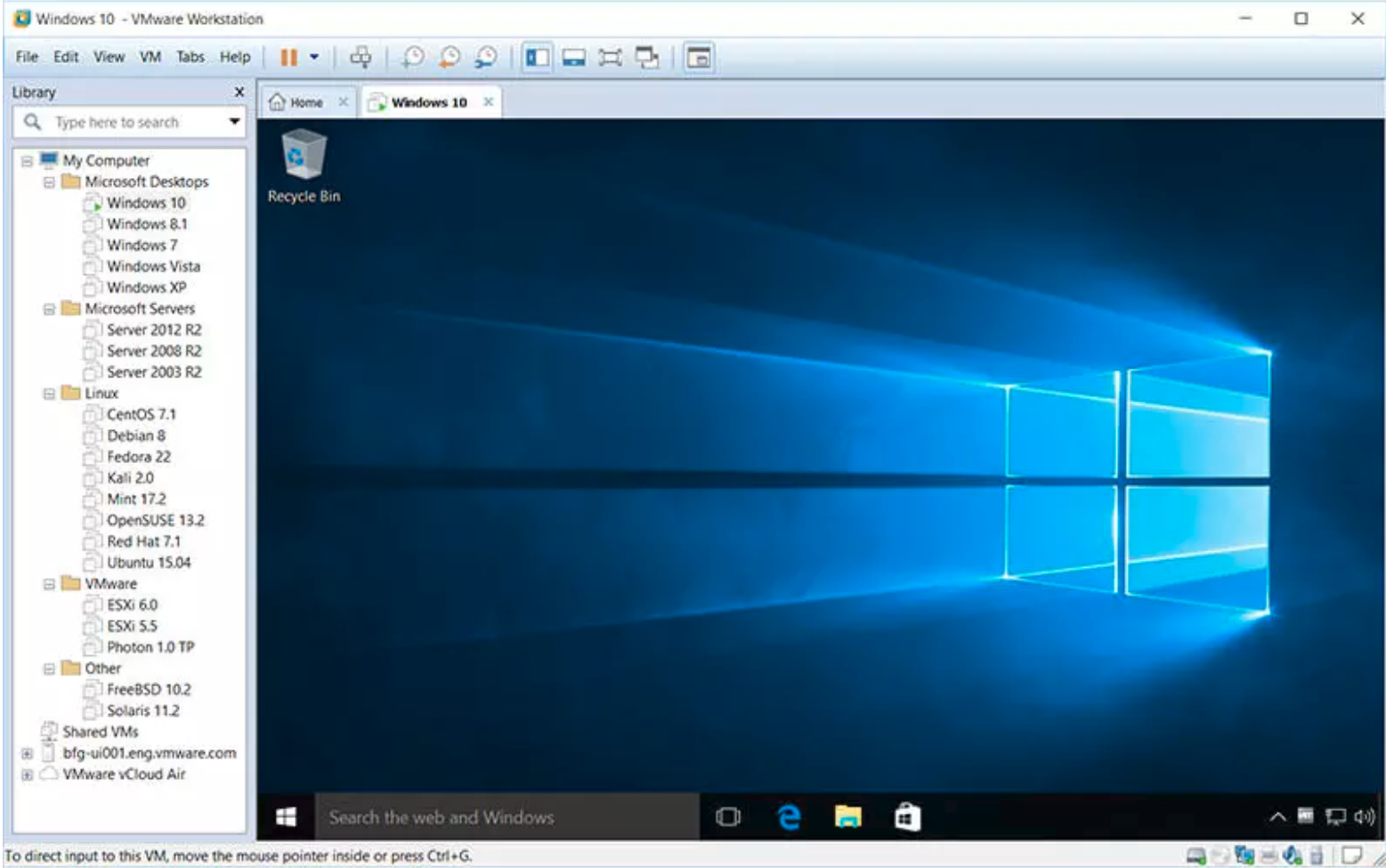
- VMware ESXi
- VMware Workstation Pro / Player (Workstation)
- VMware Fusion Pro / Fusion (Fusion)
- VMware Remote Console for Mac (VMRC for Mac)
- VMware Horizon Client for Mac
Solution
We recommend that users install the latest patches in a timely manner to avoid being hacked.





